Virtual Event, 12-14 October 2021
What is the Internet Identity Workshop?
IIW is run as an “Open Space un-Conference”, designed to be a dynamic, participant-led 'marketplace of questions and topics', to foster conversation, networking and learning. Empowering everyone to speak, ask and present, this format takes partial inspiration from decentralized approaches to technology. Collectively, attendees set each day’s agendas, volunteering a mix of prepared presentations, open discussion, product demos and workshops. Hundreds of attendees, including a number of DIF members, put together a huge programme of content for the 33rd IIW, covering topics ranging from the technical minutiae of IAM and SSI to big-picture discussions about ethics and strategy, and participated in over 110 virtual sessions across the three days.
A book of proceedings, containing the notes from all of the sessions will be collated and published by IIW (back catalogue from previous IIWs here, and a wiki of notes from individual sessions here). Here we will overview a few of the topics discussed and sketch out some of the strong and weak signals discernible in the collective discussion. To that end, sessions are clustered thematically and not chronologically.
101 Sessions
A staple of IIW, 101 Sessions are conceived as entry-level primers, often given by the same IIW veterans year after year, on various aspects of the digital identity landscape. They are designed to give participants a solid base from which to engage fully with the rest of the programme. 101 Session topics this year included OAuth2 101, UMA 101, OpenID Connect 101, with DIF’s own Chris Kelly and Karyl Fowler (Transmute, DIF Steering Committee) presenting an SSI 101 session on Self-Sovereign & Decentralized Identity.
Governance & Ethics
Informing the whole framing of this technical revolution is a broader, more conceptual sea change. Ever-popular themes for discussion include the ethical underpinnings of decentralized identity, and the increasing awareness of potential pitfalls.
The contours and workflows of identity in the digital age are largely molded by government regulations around privacy, security, and their historic interest as one of the main issuers of identification documents. For this reason, analyses of policy tendencies and direction are in close dialogue with the design of products and infrastructure, which has long been a hallmark of this particular unconference.
Ethics & Equity
Identity veteran Adrian Gropper led an indefatigable series of sessions each focused on an interlocking important concern about how identity technologies change how we understand, exercise and protect fundamental human rights across a variety of systems with Human Rights Impact of Identity Protocols. Privacy, a pillar of the decentralized identity movement, got discussed in terms of the Kantara Report, at John Wunderlich’s Privacy Enhancing Mobile Credentials session.
User choice, data portability and consent also sparked lively discussions with Adrian Gropper and Alan Karp’s session on Policy Managers and John Phillips’ session on Designing for Consent. The ethics of making any of the above mandatory at DID Ethics & Mandatory Vaccine Passports with Timothy Holborn to corona section?
Governance of SSI systems
The oversight and governance of the decentralized identity community got plenty of attention, as Open-Source organizations like DIF and ToIP introduced themselves and spoke about the work they facilitate. This discussion continued on the topic of Interop(erability) and where the appropriate venue is to continue this valuable work (Kai Wagner, Andreas Freitag, Hakan Yildiz, Eugineu Rusu).
Decentralized Identity tech also offers exciting new possibilities itself for governance, democracy, humanitarian aid and education, as discussed by Drummond Reed, cheqd’s Alex Tweeddale & YOMA’s Nicky Hickman, imagining what the Future of Governance using these tools might look like. YOMA’s work on an interim Governance Framework in Africa, which is ultimately built on ToIP’s Governance Metamodel Specification, was examined as one example.
The ongoing effort by the Blockchain Advocacy Coalition to get Verfiable Credentials (VCs) and trust frameworks recognized within Californian legislation was outlined by Kaliya Young and Ally Medina at Verifiable Credentials Policy Committee - Come Help us Pass a Trust Framework in California, identifying challenges and a path forwards towards greater legal and institutional acceptance for VCs.
Covid, Health, Travel
Corona has been a driving force recently in the decentralized identity space, particularly with regard to health and vaccination records, as well as greatly affecting travel. How decentralized identity tech like smart contracts and DIDs can empower individuals and give them granular control over their health data was tackled in Elias Strehle’s session, entitled Controlling your medical data via DIDComm - discussion and feedback on our system architecture.
Building on this system architecture theme, and the challenge of how to deal with varying forms of data arriving from a variety of sources, was teased out at Semantic Interoperability with Layered Schemas and Semantic Pipelines with Burak Serdar, who invited us to test a live, interactive Layered schema playground that manipulates and edits the various layers as defined by metadata, and then rounding off by considering the implications of this for the storage of digital healthcare data.
Linux Foundation Public Health launched the Global COVID Certificate Network in June 2021 to enable interoperable and trustworthy verification of COVID certificates between jurisdictions, based on a global trust architecture. Lucy Yang and John Walker outlined the state of this initiative at Updates on the Global COVID Certificate Network, while they were also joined by Kaliyah Young for COVID Credentials: How to Meet the Market Where it is, to join community leaders of the COVID Credentials Initiative (CCI) reviewing the state of play and obstacles to adoption
VC-centric Technical sessions
Verifiable Credentials (VCs) were an inescapable topic at IIW33, both following up IIW32’s strong theme of roadmapping adoption of BBS+ signing systems for selective disclosure and more generally educating people about the 4 flavors of VCs and how they interact.
Vc tooling and education
Sometimes the best thing to do is lead by example, and Kyle Den Hartog presented his Working with JSON-LD - Best practices and improvements (DECK) along with proof of concept code (GitHub) to demonstrate how handling JSON-LD data can be done elegantly. As a strong theme at the last two IIWs was that LD-VCs have a steep learning curve and require a 90-degree turn in many approaches to credentialing and data exchange, this will surely be remembered as one of the most useful and educational sessions of the conference.
At An Extended LDP-BBS 2020 and ZKP-LD Playground, Dan Yamamoto & Kazue Sako dove even deeper into the operation of BBS+ protocols and zero-knowledge proofs. The tagteam recently forked Mattr’s BBS+ LD implementations and were presenting on strategies for handling the “multiple blank node” problem, a common stumbling block in signing over flattened graphs. Attendees were invited to a ZKP LD playground to test their approaches.
Updates from the OIDF/DIF collaboration:
Kristina Yasuda, Torsten Lodderstedt started us off by considering generally Open ID Connect for SSI, examining some potential benefits, and comparing the typical OIDC flow to a more SSI-led Self-Issued OpenID Connect Provider (SIOP) model. Kristina and Torsten returned, this time joined by Oliver Terbu and Tobias Looker, to give us an insight into the OIDF work towards a protocol suite for SSI at their session on VC Issuance using OpenID Connect, while considering the potential of the OpenID protocol and how it operates with existing frameworks luke FIDO 2 or Microsoft and Apple’s authentication methods.
Verifiable Credentials versus Mobile Driver’s Licenses (mDL)
Andrew Hughes (Ping Identity) did a series of sessions on Mobile Driving License AND Verifiable Credentials laying out the basics of mDocs (mobile driver's license) as currently released, including the OIDC/web transport specification, and how the data model and protocols could co-exist and whether they should. Discussion here was predominantly about ISO 18013-5, a new ISO standard designed to primarily specify a driving license data models, protocols, and security models, which has led to renewed interest in digital forms of electronic ID (eID) credentials issued by and closely regulated by state identity authorities.
VC adoption vectors
No new technology can get off the ground without some consideration about how and where it gets adopted and implemented. Trinsic’s Ben Crockett kicked off with an overview of the global playing field, in his Global Verifiable Credential Adoption session. Newly-minted DIF members cheqd presented Payment rails, customisable commercial models and decentralised governance for SSI, which gave Fraser Edwards & Alex Tweeddale a chance to examine roadblocks, in particular the lack of commercial models, in the adoption path for SSI models and payment systems. They rounded this off with cheqd’s vision of being the one to bridge this divide.
The Universal Registrar and Friends
Longtime DIF insider Markus Sabadello introduced the IIW community to DanubeTech's new commercial offering GoDiddy.com (based squarely on two of DIF's oldest work items, the Universal Resolver (and Universal Registrar), following the classic "hosted service, open-source self-hosting option" formula; DanubeTech also gave additional technical sessions about these work items. The Universal Resolver Work Item was recently folded back into the main DIF Identifiers & Discovery Working Group, where work continues. Markus was joined by Azeem Ahamed and Cihan Saglam to discuss DID Registration Architectures more generally, discussing considerations for working with CRUD methods while remaining architecture-neutral
Other Technical Sessions
Sam Curran led a session on-boarding interested community members to the protocol work being organized within and on top of DIDComm. The session was named Fantastic DIDComm Protocols, and How to Write Them because the focus was on DIDComm protocols as a community-driven toolkit where sub-protocols and extensions are contributed organically by users, and users discuss design issues and implementation issues with one another in a forthcoming User Group, which provides an “outer circle” to the DIDComm Working Group (which will continue on after the completion of the v2 specification to manage the iteration of the DIDComm and the related protocols in an IPR-protected venue).
The DIDComm reference implementations Session with Alex Scherbakov and Vyacheslav Gudkov gave newcomers to the space a crash-course on DIDComm v2 and DID:Peer, while extolling the virtues of reference implementations for emerging specifications. They also illustrated how basing these implementations on established libraries is important to ensure interoperability with a live DIDComm demo.
DIDComm was one primary use-case but not the only possible use case discussed by Oliver Terbu and Alen Horvat in a session called “LibP2P as transport layer,” which explored the possibilities of the DIDComm mediator networks and other lightweight infrastructure crucial to SSI systems being spun up in a peer-to-peer way. The libp2p library, which came out of the IPFS stack for decentralized storage and has found a lot of adoption in blockchain for other peer-to-peer applications and communication transports, could end up being crucial as more infrastructure moves out of centralized clouds and into more organic distributed systems.
Picos (persistent compute objects) are DIDComm-enabled agents supporting SSI. Picos, DIDComm, and Decentralized SSI Agencies from Phil Windley explores the potential of these microservices, aligned with many of the design goals of decentralized identity, and how they could function as nodes for a scalable Internet of Things (IoT) model.
DID AuthN WG without DIDs
Surprisingly, one of the best-attended sessions at this IIW wasn’t about the DID/VC stack at all, but rather about the Ethereum stack so central to the work of Consensys, Affinidi, Ceramic, and many other DIF members. As part of a grant from the Ethereum Foundation and in collaboration with the Ethereum Name Service (a registrar for linking ethereum addresses to a DNS-like record system), Spruce has been been driving a design process for Sign-In With Ethereum informed by community calls to harmonize how relying parties within the Ethereum community request an “off-chain signature” to log into services and create sessions. Both chairs of DIF’s DID Authentication WG (which has not been holding regular meetings while focusing on the Authentication aspects of the DIF/OIDF specification work) have been participating, as have DIF members Ceramic; work is ongoing and an alpha release will be available soon.
User Journeys & Product Thinking
Strategies For Bridging to Next-Generation Identity Systems (from the bottom up) from David Schmudde outlined some potential solutions to e-commerce challenges using VCs, OAuth and OpenID Connect (OIDC). Conversations and topics arising at each IIW often make a reappearance at a later session, and Phil Wolff’s UX: continuing the mid-2021 IIW UX conversation, revisited a UX design session held at IIW32 in April of this year. A unified tech framework ideally needs to be complimented by a common visual language, as well as a standardized way of describing the tools and processes involved.
Devices & users
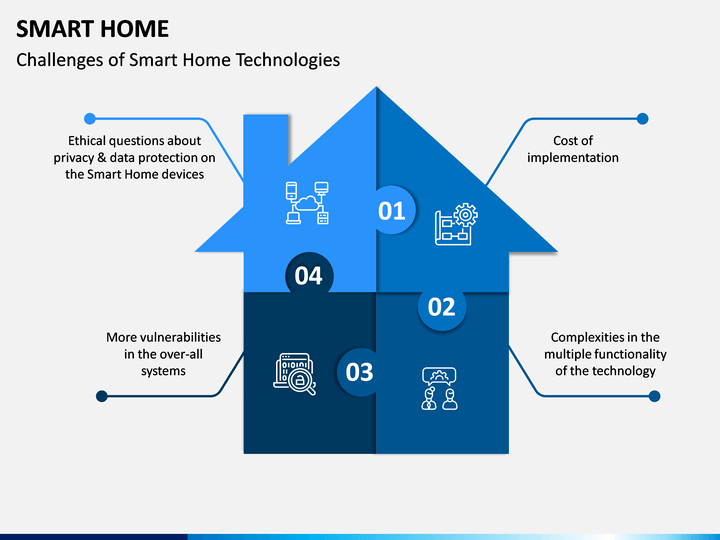
Considering end-users’ experiences and which devices they use to access new technology is also incredibly important. To this end, IIW co-founder Doc Searls, along with Joyce Searls and Johannes Ernst hosted User Stories for the VRM Intention Byway. The Intention Byway presents an alternative vision for how buyers and sellers in a decentralized marketplace can reach one another with their offerings. Bridging Digital and Physical to Make Identifiers Identify by Liam McCarty discussed both the technical challenges between varying device types, while underscoring the need for consumer, community and business interest in decentralized tech to attain widespread adoption and trust. IoT and Smart Homes add to the growing number of entities online that will need an ‘identity’, and digital assistants as mediator for ‘communal computing was outlined by Chris Butler at Is the smart home a dictatorship, co-op, or homesteading?
Organizational Bread-breaking
At Time is Running Out - Get to Market: revenue, costs and who pays for what, Kimberly Linson argues that without a convincing business case, adoption of new tech may be slow or even stall, and the financial cost of implementation needs to be borne by someone. Phil Wolff hosted VC Metaphors - Containers and ? to discuss how we can agree on a common language around this emerging technology and how it can be easily presented to policy-makers, customers and businesses alike. In a similar vein, Kaliyah Young used two separate sessions dedicated to Explainers Needed to host an open discussion about where the knowledge or vocabulary gaps are around decentralized identity tech, and how and where we should fill them. The huge number of ideas to come out of these sessions will provide a wealth of informational content for the sector, important for making it cohesive and accessible.
Karim Stekelenburg, James Ebert and Timo Glastra used Taking the adoption of SSI to the next level to discuss how this conversation also needs to extend to developers, who may not necessarily already be involved in the digital identity space. Ample documentation, open-source communities and extendable functionality of frameworks were just some of the resources name-checked to make the sector welcoming beyond the enthusiasts and dedicated groups seen at spaces like IIW. Illustrated use-cases, specifically one based on Aries and written in JavaScript was highlighted for using familiar, stable and well-documented APIs to improve accessibility.
Other User-Centric Data Orgs
Lisa LeVasseur, at Identification Minimization and other Respectful Tech Principles, explored how decentralized identity solutions can offer increased security, privacy and anonymity. The discussion centered around minimizing user data collection, under the umbrella idea of ‘respectful’ tech design principles, as outlined by the Me2B Alliance’s Attributes for Respectful Me2B Commitments. Lisa returned with Scott Mace to introduce attendees to the IEEE P7012 working group at Privacy Signal Standard Update (IEEE P7012), the standard for machine readable personal privacy terms. Again, Lisa shared a framework out of the Me2B Alliance to illustrate how P7012 can matter in the arc of a digital relationship, such as between an individual and a web site.
ToIP
Judith Fleenor presented an Introduction To Trust Over IP, introducing ToIP, and reviewing their first year as part of the digital identity community, focussing on not only the technical questions around decentralized identity, but also accountability on the legal, business and social impact layers. Neil Thomson gave an overview of one cluster of related work items at ToIP entitled VCs Meet Reality: Custom VC Evaluation with Privacy that went into the weeds on the nuances of progressive disclosure and privacy considerations of complex, real-world use-cases involving sensitive personal data requiring consent receipts and the like. This work was partly done in the context of the Brussels-funded ESSIF-LAB incubator project, which allowed European startups (many of them DIF members) to collaborate on privacy and regulatory compliance issues specific to the European context.
Next Steps
Many thanks and much praise to the dedicated team at IIW for running a virtual event of this scale, and providing a virtual venue for such vibrant exchanges and discussion. As always, the conversations at IIW are like games of jump-rope: you can jump in and out at any time with a little tact and coordination. Many of these conversations happen at DIF, or have touchpoints with DIF that give periodic updates at DIF meetings, and the upcoming DIF Face-to-Face in early 2022 will include major updates from many of these. In particular, DIF’s community of practice for Product Managers and UX professionals is actively seeking discussion topics and presentations to keep the momentum going between IIWs and DIF F2Fs, so do join the mailing list and reach out if you’d like to discuss product ideas, user stories, and UX quandaries. As always, the best way to keep up-to-date, gain insight and learn-while-doing is to get involved directly with the open-source decentralized identity community.
